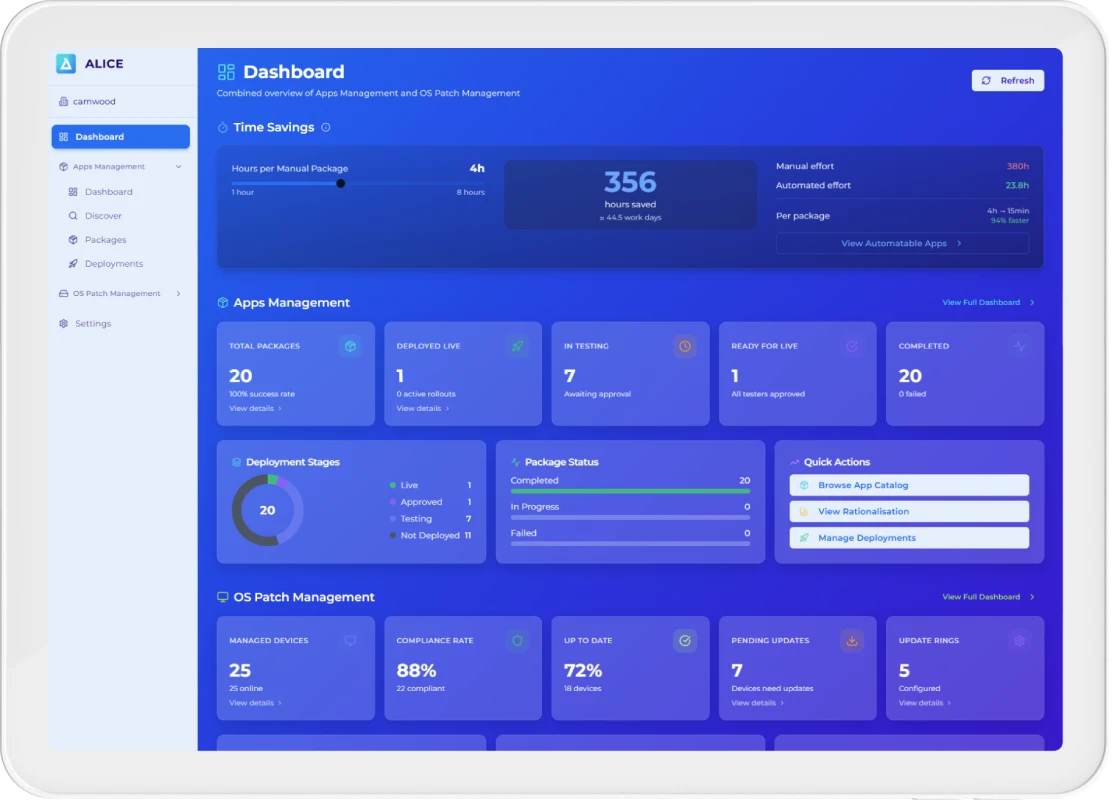
The only platform built for automated application lifecycle management — from estate discovery and rationalisation to packaging, phased deployment, and hands-off auto-updates — built natively on Microsoft infrastructure.
Connect to your Microsoft Intune environment. See your normalised, rationalised estate in under 10 minutes.
To connect ALICE to your Microsoft environment and see your first insights
Used in complex enterprise and post-M&A environments
ALICE extends your existing Intune and SCCM investment, not replaces it

Supports compliance across your entire application estate
Transparent, scalable, no hidden infrastructure costs

Most enterprise IT teams are managing blind. Manual audits take months, cost hundreds of thousands of pounds, and are out of date before they’re finished. Every unmanaged application is a potential CVE exposure, a compliance gap, or unnecessary cost buried in your estate.
ALICE eliminates every one of these problems — automatically.
ALICE is the Application Lifecycle Intelligence & Compliance Engine — a cloud-native platform that connects to your Microsoft Intune environment via Graph API, pulls your full detected application inventory, and automates the entire lifecycle from discovery to retirement.

Complete, continuously updated visibility across every installed application

11,400+ app database normalises, rationalises, and identifies functional duplicates automatically

CVE database cross-referencing surfaces vulnerable and end-of-life applications instantly

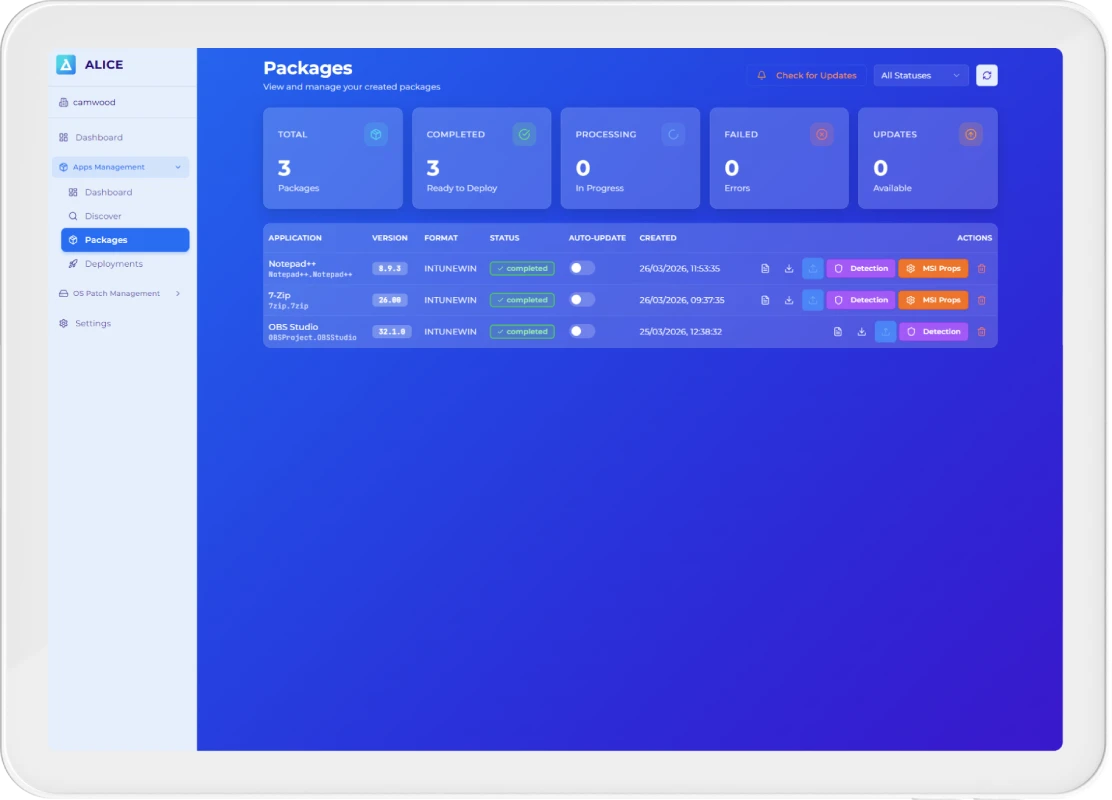
PSADT v4 packages generated automatically; phased 10%→50%→100% rollouts with tester approval gates

Version monitoring, automated repackaging, and deployment when new versions are released

Full data isolation per tenant; unified cross-tenant visibility for post-M&A environments
ALICE guides your application estate through seven structured stages — from first connection through to fully automated, always-on lifecycle management.
ALICE deploys via a lightweight, cloud-native approach — no on-prem infrastructure, no complex networking, and no lengthy configuration cycles. Connect your Azure AD app registration and ALICE begins discovering your estate immediately, normalising display names and mapping every installed application to the exact devices running each version, across on-premises, remote, and hybrid endpoints.
Outcome:
A live connection to your entire application and endpoint estate.
ALICE performs continuous discovery via Microsoft Graph API, pulling every installed application from Intune and normalising display names into unified application families — collapsing every version variant into a single row. Every version is mapped to the exact devices running it, giving your team a complete, always-current view of the entire application estate across all endpoints.
Outcome:
A single, continuously updated source of truth for the application estate.
ALICE cross-references your estate against 11,400+ curated entries, automatically removing system components, drivers, and redistributables. Functional duplicates — two PDF readers, three remote desktop tools — are surfaced for consolidation. Once the approved list is confirmed, ALICE auto-generates a PSADT v4 package per application, compiles it to IntuneWin, and uploads to Intune, removing older vulnerable versions.
Outcome:
A clean, standardised, vulnerability-reduced estate ready for governed lifecycle management.

Each application is assigned an owner, a lifecycle status (keep, retire, replace, investigate), and a risk classification of High, Medium, or Low. Applications follow structured install → update → review → retire workflows enforced automatically by ALICE. Version exclusions, CVE flags, and compliance posture are tracked continuously, with audit-ready reporting always available on demand.
Outcome:
Clear ownership, standards, and accountability across the entire estate.
With governance in place, ALICE enforces application-driven automated patch management. OS patching rings are created automatically based on application risk, ensuring devices running high-risk applications are patched first. Once a canary group meets the configured success threshold, the next phase deploys without manual intervention. Automated validation and rollback reduce deployment risk throughout.
Outcome:
Drastically reduced vulnerability windows and a stable, secure environment.


Application packaging, update cycles, lifecycle reviews, compliance reporting, and estate hygiene all become fully automated. ALICE’s background scheduler monitors Intune success rates and auto-progresses deployments through each phase. App owners receive email notifications at every phase transition — whether triggered manually or by the scheduler — and IT scales without adding extra headcount.
Outcome:
Higher reliability, lower operational effort, and an IT function that scales with the business.
In BaU, ALICE operates as an always-on intelligence layer. New applications are discovered and classified automatically. New versions are detected via the Winget repository, packaged through the same PSADT pipeline, pushed through tester approval, and deployed in phases — all without human intervention. Every package is stored in your own Azure Blob Storage, ensuring full ownership and auditability.
Outcome:
A simplified, secure, compliant, and fully optimised estate — managed automatically, every day.


You manage only approved applications

Only current, secure versions are deployed
Legacy vulnerabilities are removed at source

Application risk, not guesswork, drives security decisions

OS patching is continuous and automated

Operations scale without manual effort


Connect via Graph API and see your full normalised estate — every app, version, and device — in under 10 minutes.

Automatic multi-pass matching against our curated database rationalises your estate on first sync.

PSADT v4 packages generated automatically — MSI properties, silent switches, IntuneWin upload included.

Controlled 10%→50%→100% rollouts. No app goes live until all assigned testers have approved.

Once configured, every new app version is packaged, tested, and deployed automatically by ALICE.

Applications cross-referenced against CVE databases daily — vulnerabilities surfaced with device-level precision.

Navigate regulatory pressure, multi-tenant complexity, and cost reduction mandates with full, continuous application estate visibility.

Maintain operational readiness with a security-first approach to application discovery, compliance, and estate control.

Manage sprawling, budget-constrained estates with tools built for compliance, efficiency, and public accountability.
For focused teams standardise a single business unit or use case
Designed to cover discovery, inventory, and application‑driven patching for a defined segment of the estate.
For organisation standardise & GOV the majority of their application estate
Adds catalogue‑driven packaging, governance workflows, and extended reporting.
For complex, regulated or multi‑tenant environments
Full lifecycle automation, advanced integrations, extended data retention, and multi‑tenant support for MSPs.
ALICE is the Application Lifecycle Intelligence & Compliance Engine — a cloud-native platform built on Microsoft infrastructure that automates the complete application lifecycle. It connects directly to your Microsoft Intune environment via Graph API, discovers your entire application estate, and normalises it using an in-house database of 11,400+ curated application entries. From there, ALICE automates packaging using PowerShell App Deployment Toolkit (PSADT v4), orchestrates phased deployment with tester approval gates, tracks CVE vulnerabilities at device level, and auto-updates applications when new versions are released — all without manual intervention.
Unlike generic patch management tools, ALICE manages the full lifecycle: from the moment an application is discovered, through rationalisation, packaging, testing, phased rollout, ongoing compliance monitoring, and eventual retirement. Every package is stored in your own Azure Blob Storage, giving your team full ownership and control. Multi-tenant architecture ensures complete data isolation between customer environments, making ALICE equally suited to single-tenant enterprises and managed service providers.
Most organisations are connected and seeing their rationalised estate in under 10 minutes of connecting. ALICE integrates directly with your existing Microsoft Intune environment — you provide your Azure AD app registration credentials, and ALICE immediately begins discovering and normalising your application estate using Graph API. There is no complex deployment, no professional services engagement, no VPN configuration, and no server infrastructure required to get started.
During your 14-day free trial, you have full access to every ALICE feature from day one. Our team will also prepare a bespoke subscription estimate based on your application count and total managed devices, delivered before your trial ends so you have full commercial clarity before making any commitment.
No — ALICE works alongside your existing Microsoft tooling. Think of ALICE as the intelligence and automation layer on top of your Intune investment: it reads your application inventory from Intune via Graph API, automates what Intune cannot do natively (packaging, phased rollouts, tester approval workflows, auto-updates), and writes packaged applications back into Intune as Win32 LOB apps. Your existing Intune policies and configurations remain unchanged.
For organisations transitioning from SCCM to Intune, ALICE provides the application readiness intelligence needed to plan and execute that migration with confidence — knowing exactly which applications are packaged, compliant, and ready to move before the cutover begins. ALICE does not rip and replace; it extends and accelerates.
Sign up at beyondapplications.io/register and connect ALICE to your Microsoft environment using your Azure AD app registration. Full access to all features is available from day one — no feature restrictions, no credit card required to start. ALICE will immediately begin discovering and normalising your application estate, surfacing your full inventory, rationalisation opportunities, and CVE exposure in under 10 minutes. During the trial, our team analyses your specific estate and prepares a bespoke pricing estimate based on your application count and number of managed devices. You receive that estimate before the trial ends — full commercial clarity, zero obligation.
ALICE is primarily used by IT Operations leads, EUC (End User Computing) managers, IT Directors, and enterprise architects in mid-to-large organisations — particularly those in regulated sectors such as Finance, Defence, and Local Government where application governance carries real operational, regulatory, and financial consequences. CIOs and CISOs value the governance reporting, compliance posture dashboards, and audit-ready outputs. ALICE is also well-suited to managed service providers managing multi-tenant Microsoft environments and organisations navigating post-merger application estate integration.
ALICE is built on Microsoft infrastructure and aligned to UK security frameworks. Every package is stored in your own Azure Blob Storage — your data never leaves your control.
The future of automated application lifecycle management starts here.
Full access. No commitment. A bespoke pricing estimate delivered before your trial ends.